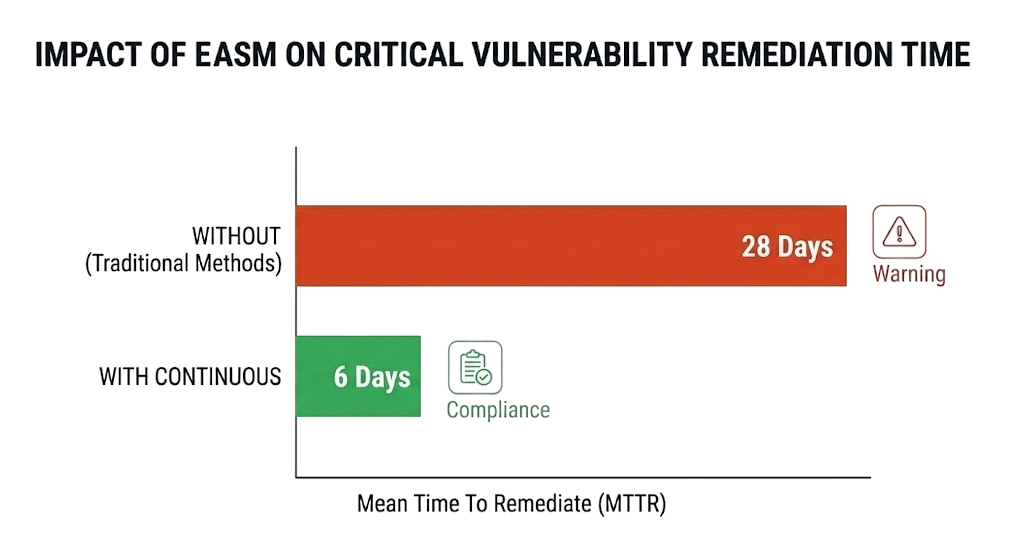
What is External Attack Surface Management?
External Attack Surface Management (EASM) is the continuous process of discovering, analyzing and monitoring all internet-facing digital assets owned by an organization. EASM platforms identify domains, subdomains, IP addresses, cloud services and APIs that could be exploited by threat actors, providing security teams with complete external visibility.