See your external attack surface the way attackers do
AUTODIT continuously discovers exposed assets and Shadow IT, prioritizes exploitable risk, and keeps NIS2 and DORA evidence audit-ready — agentless, with AI-driven analysis.
EASM · Continuous monitoring · GDPR compliant
Your External Attack Surface Changes Faster Than Manual Audits
Traditional security assessments miss the essential point: the unknown, applications and vulnerabilities are constantly evolving.
Shadow IT
Employees deploy unauthorized cloud services, SaaS tools and test environments that security teams never see.
Forgotten Assets
Legacy servers, expired subdomains and abandoned applications remain exposed long after projects end.
Exposed Services
Open ports, misconfigured APIs and unprotected admin panels create entry points for attackers.
Leaked Secrets
API keys, credentials and tokens published in code repositories or public documents.
Compliance Drift
Security configurations degrade over time, causing silent deviations from NIS2, DORA, ISO 27001 and GDPR requirements.
Comprehensive Attack Surface Management
Powered by AI to minimize false positives and maximize actionable security insights.
Attack Surface Discovery
Discover internet-facing assets continuously. Map domains, subdomains, IPs, open ports and cloud services across your entire perimeter.
AI Risk Prioritization
Rank vulnerabilities by exploitability and business impact. Focus remediation on threats that matter most to your organization.
Secret Exposure Detection
Detect leaked credentials, API keys and tokens across code, public documents and exposed configurations.
Compliance Monitoring
Track deviations from NIS2, DORA, ISO 27001, GDPR and PCI-DSS continuously. Generate audit-ready evidence reports.
How AUTODIT Works
From asset discovery to continuous monitoring — five steps to complete attack surface visibility.
Discover
Automated enumeration of all external assets: domains, subdomains, IPs, cloud services and shadow IT.
Analyze
Deep vulnerability scanning with CVE detection, misconfiguration checks and compliance verification.
Prioritize
Risk scoring based on exploitability, business context and threat intelligence.
Remediate
Actionable recommendations with reproduction commands and evidence-backed remediation steps.
Monitor
Continuous monitoring with proactive alerts on new exposures and configuration changes.
Cybersecurity Threat Report
Download our Cybersecurity Threat Report and outlook for 2026.
A comprehensive analysis of the evolution of threats by sector and by country.
Learn how to protect your assets from the latest threats and be compliant with the latest regulations.
Built for Security Decision Makers
Tailored workflows for every role in your security organization.
You are responsible for ensuring compliance. The deadlines are approaching.
NIS2, DORA, ISO 27001 — each regulation requires continuous monitoring. AUTODIT automatically generates the accepted evidence for your certification audits.
- NIS2 Article 21 report exportable with one click.
- Continuous monitoring of security posture vs. annual monitoring: demonstrate progress between audits.
- Executive dashboard for your monthly management committee reporting.
- Immediate alerts on exposed assets.
AUTODIT enabled us to present our NIS2 compliance with an automatically generated report. This is the first time our auditor has had no comments on the documentation.
Defend your security budget at the Executive Committee meeting. With figures.
An external audit costs between €15,000 and €80,000, for a snapshot at date T. AUTODIT replaces this expense with continuous monitoring at a fraction of the cost.
- Calculable ROI: savings vs. annual external penetration test.
- Complete visibility across your perimeter without mobilizing your team.
- API integration with your ticketing system (Jira, ServiceNow).
- Shadow IT report for arbitration of unapproved projects.
We were spending €40k/year on two penetration tests. With AUTODIT, we have permanent coverage and I've redirected the budget towards remediation — where it really matters.
Spend more time fixing problems than sorting through false positives.
Our AI engine eliminates 78% of false positives by contextualizing each vulnerability. You only see what truly matters — with remediation steps directly in the report.
- Automatic prioritization based on actual usability (not just CVSS).
- AI-generated remediation steps with proof of fix.
- Scan in 2 to 60 minutes depending on the perimeter.
- Export to Excel and PDF for integration into your workflows.
We used to have 300 alerts per week. Now we have 18, all actionable. AUTODIT's AI has changed the way we work.
A large share of data exposure starts from shadow IT assets the company never knew it had
External Attack Surface Management (EASM) as a mandatory prerequisite?
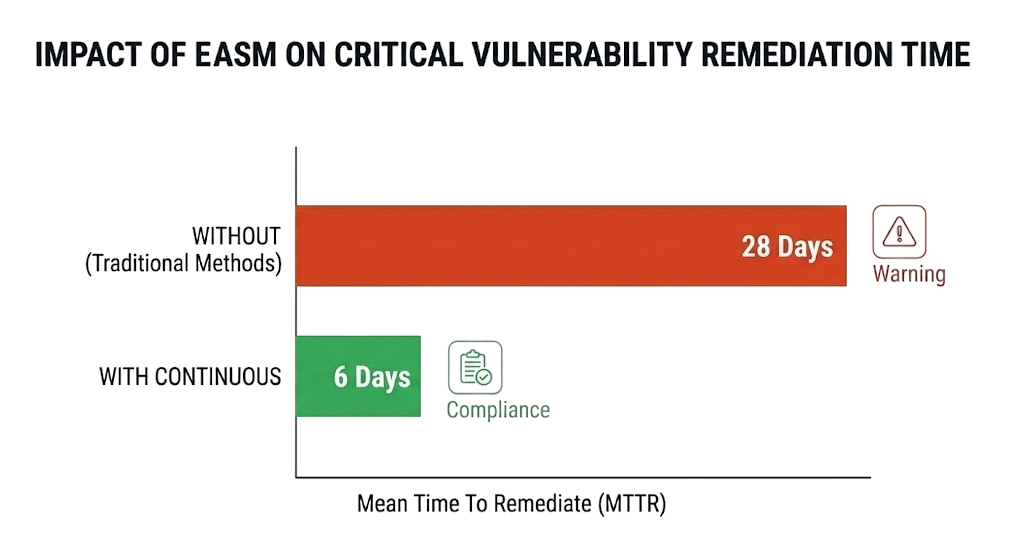
Continuous Visibility: Unlike an annual penetration test, EASM monitors exposure 24/7.
Attacker's View: It allows you to see your infrastructure exactly as a hacker sees it.
Prioritization: In 2026, it's impossible to fix everything. ASM helps prioritize vulnerabilities that can be exploited immediately.
Cost-Effective: AI-powered prioritization reduces wasted time and resources on low-risk issues.
Compliance: Stay ahead of regulations with continuous monitoring and automated reporting.
Continuous coverage at a fraction of an annual pentest
Illustrative comparison of point-in-time testing versus continuous monitoring. Figures are directional ranges to frame the trade-off — not measured customer averages.
| Indicator | Before AUTODIT | With AUTODIT | Gain |
|---|---|---|---|
| Time on audits | 100-150 h / year | 25-40 h / year | -70 % |
| Critical vulnerabilities | 4-7 per quarter | 15-25 detected | +250 % visibility |
| Compliance deadline NIS2/DORA | 3-5 months | 2-4 weeks | ×4 faster |
| False positives | 30-40 % | <5 % | Team refocused |
Calculate your savings
How AUTODIT Compares
See how continuous AI-powered monitoring outperforms traditional approaches.
| Capability | AUTODIT | Traditional Pentest | Legacy ASM |
|---|---|---|---|
| Continuous monitoring | ✓ Automated | ✗ Point-in-time | ◐ Periodic scans |
| Prioritization | ✓ Context-aware AI (reports) | ✗ Manual triage | ◐ Rule-based |
| Proactive alerts | ✓ Instant notifications | ✗ Report after weeks | ◐ Delayed alerts |
| Scalability | ✓ Unlimited assets | ✗ Per-engagement | ◐ License-limited |
| Automation | ✓ Fully autonomous | ✗ Manual testing | ◐ Semi-automated |
| Cost efficiency | ✓ Predictable SaaS pricing | ✗ High per-test cost | ◐ Complex licensing |
Gallery
Explore the security outcomes you need
Use the landing page for the overview, then go deeper into the exact problem, framework, or operating model your team needs to solve.
Attack Surface Management platform
Get a focused view of how AUTODIT discovers exposed assets, maps internet-facing risk, and supports continuous external monitoring.
See the EASM pageShadow IT discovery
Understand how to uncover unknown domains, forgotten services, and unmanaged exposure before they become incidents.
See the Shadow IT pageNIS2 compliance monitoring
Turn continuous external monitoring into usable evidence, reporting, and prioritization for NIS2 programs.
See the NIS2 pageDORA compliance monitoring
Support resilience and third-party risk programs in finance with continuous visibility across exposed assets.
See the DORA pageSee how the platform fits different environments
Industry pages help buyers connect the same monitoring model to sector-specific exposure, resilience, and governance needs.
Financial services security monitoring
Connect external exposure, resilience reporting, and third-party risk to finance-specific security operations.
See the finance pageHealthcare security monitoring
Support healthcare environments with better visibility into exposed services, legacy risk, and digital trust.
See the healthcare pageSaaS attack surface monitoring
Help fast-moving SaaS teams manage cloud sprawl, customer-facing exposure, and external release risk.
See the SaaS pageWhat good looks like with AUTODIT
Representative scenarios built from common situations our buyers describe. They illustrate how the platform is designed to be used — they are not individual customer endorsements.
A regional bank preparing a NIS2 audit uses continuous discovery to surface forgotten internet-facing assets its CMDB never recorded, then exports a PDF report that maps findings to the evidence auditors ask for.
An industrial group consolidates discovery, prioritization, and reporting into one platform — less alert noise to triage and fewer overlapping tools to maintain.
A healthcare provider relies on typosquatting and brand-impersonation monitoring to flag lookalike domains early, so a phishing campaign can be reported and taken down before it reaches patients.
Frequently Asked Questions
What types of vulnerabilities are you detecting?
We scan for SSL/TLS vulnerabilities, DNS misconfigurations, open ports, security headers, exposed files, known CVEs and many other OWASP and MITRE vulnerabilities.
How long does a scan take?
A full scan (discovery, penetration testing, compliance, and SEO) can take between 5 and 60 minutes, depending on the scope and performance of the target. Quick scans are completed in less than 5 minutes.
Can I integrate AUTODIT into my SIEM or ticketing tool?
Yes. AUTODIT exposes a full REST API and MCP. Jira and ServiceNow integrations are possible depending on your Jira and ServiceNow licenses. SIEM integrations (Splunk, Elastic, QRadar) require a connector or custom development.
Do you offer customized packages?
Yes! Contact us for customized business pricing with dedicated support, SLA and deployment options.
Do I need authorization or an agent to scan?
No agent is required. AUTODIT works from an external, attacker-side view, so you only scan assets tied to domains you own or are authorized to assess. First discovery results typically appear within hours.
Where is my data hosted and is it GDPR-compliant?
AUTODIT is a French platform and processes data in line with the GDPR. Data residency and hosting details for regulated or sovereignty-sensitive buyers are available on request.
How is AUTODIT different from a traditional vulnerability scanner?
A scanner checks assets you already know about. AUTODIT first discovers unknown internet-facing assets and Shadow IT, then assesses them — so you find exposure that never made it into your inventory.
How do you prioritize which vulnerabilities matter?
Beyond CVSS, AUTODIT factors in real-world exploitation signals such as CISA KEV and EPSS, plus business context, so teams focus on what is actually exploitable instead of chasing every high score.
Will scanning disrupt my production systems?
AUTODIT uses non-intrusive, external discovery and assessment designed to avoid impact on production. It observes what is exposed rather than launching disruptive exploitation.
Which compliance frameworks does AUTODIT support?
AUTODIT helps produce continuous evidence for NIS2, DORA, ISO 27001, GDPR, PCI-DSS, and SOC 2 by keeping a current view of exposed assets, weaknesses, and remediation progress.
Your data, our priority!
As a security partner, we apply the strictest market rules.
AES encryption per client
Each client has their own encryption key. Your data is strictly isolated and inaccessible to other tenants.
100% European hosting
All our servers are hosted in Europe by European providers.
Secure AI
Data used by AI is not used to train AI. No sensitive data is transmitted to third parties.
Secure Your Attack Surface Today
Continuously detect exposed assets, misconfigurations and compliance gaps before attackers exploit them.