Stop Vulnerabilities Before They Become Breaches
Gain visibility through in-depth AI-based vulnerability and compliance testing, monitoring of your e-reputation and typosquatting, with automated evidence reports for your certifications.
Beyond Standard Scanning
Powered by our AI engine for low false positives, no time wasted, only important action to ensure the best security measure and cost effective.
-
Deep AI-based Vulnerability ScanningOur AI engine analyzes your digital assets to detect vulnerabilities with high accuracy including CVE detection and minimizing false positives.
-
Compliance and SEO checkingEnsure your website complies with industry standards (GDPR, PCI-DSS, SWIFT, HIPAA, SOC2, ISO 27001, DORA and NIS2). Check search engine optimization best practices and gain visibility.
-
E-reputation, and typosquatting monitoringMonitor your online reputation to detect potential identity theft or compromises. Detecting typosquatting before it is exploited by malicious actors.
-
Shadow IT discoveryDiscover hidden assets and shadow IT across your organization.
-
Evidence detailled reportsReceive comprehensive, AI-generated reports with actionable insights and evidence.

30% of data leaks originate from shadow IT assets that the company was unaware it possessed
External Attack Surface Management (EASM) as a mandatory prerequisite?
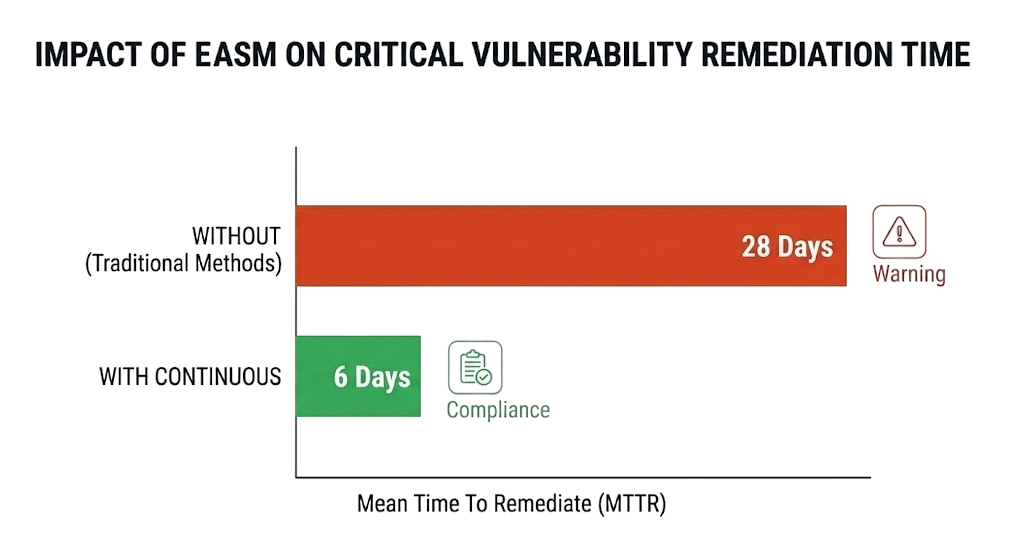
Continuous Visibility: Unlike an annual penetration test, EASM monitors exposure 24/7.
Attacker's View: It allows you to see your infrastructure exactly as a hacker sees it.
Prioritization: In 2026, it's impossible to fix everything. ASM helps prioritize vulnerabilities that can be exploited immediately.
Cost-Effective: AI-powered prioritization reduces wasted time and resources on low-risk issues.
Compliance: Stay ahead of regulations with continuous monitoring and automated reporting.
Cybersecurity Threat Report
Download our Cybersecurity Threat Report and outlook for 2026.
A comprehensive analysis of the evolution of threats by sector and by country.
Learn how to protect your assets from the latest threats and be compliant with the latest regulations.
How It Works
Get comprehensive security insights in three simple steps
Subscribe to a plan
Choose the plan that fits your security needs. No hidden fees.
Launch the scan
Our distributed probes perform a complete security analysis based on your plan and the chosen scan.
Get the results
Receive detailed results with remediation advice.
Gallerie
Data Protection
Because your data is our priority, we implement the best security measures to protect your data.
Sensitive Datas
Sensitive datas are AES-encrypted per client and accessible only to you.
Data Location
Our data servers are located in Europe, but on request, dedicated servers can be deployed in your country with the Enterprise license.
AI Security
All our AI models are protected by the best security measures to prevent any data breaches. They are local models no API connection to any providers like OpenIA, Antropic, Google or X.
Scale Your Protection
Choose the plan that fits your security needs. No hidden fees.
Free Trial
Get started with basic scans
- 3 Free Targets scans
- E-Reputation
- TLS/SSL
- Basic vulnerability detection
- Compliance check (GDPR, PCI-DSS, SWIFT, HIPAA, SOC2, ISO 27001, DORA and NIS2)
- SEO
- EASM Monitoring (include Shadow IT Discovery, Typosquatting detection, CVE Monitoring)
- API integrations
- Excel Export
- 30-day testing period
- Email notifications
- Default support
Pro
Advanced scans for professionals
- 10 Targets with limited scans
- E-Reputation
- TLS/SSL
- Advanced vulnerability detection
- Compliance check (GDPR, PCI-DSS, SWIFT, HIPAA, SOC2, ISO 27001, DORA and NIS2)
- SEO
- EASM Monitoring (include Shadow IT Discovery, Typosquatting detection, CVE Monitoring)
- API integrations
- Full detailed results PDF and Excel
- 1-year result retention
- Email notifications
- Silver support
Enterprise
Custom solutions for large organizations
- Unlimited scans
- E-Reputation
- TLS/SSL
- AI Powered vulnerability detection
- Compliance check (GDPR, PCI-DSS, SWIFT, HIPAA, SOC2, ISO 27001, DORA and NIS2)
- SEO
- EASM Monitoring (include Shadow IT Discovery, Typosquatting detection, CVE Monitoring)
- API integrations
- AI Powered results PDF and Excel
- Custom result retention
- Email notifications
- Gold support
* Price includes VAT. Minimum 12-month commitment, one-time payment with automatic renewal or monthly without discount.
Available Optional Features.
Frequently Asked Questions
What types of vulnerabilities do you detect?
We scan for SSL/TLS issues, DNS misconfigurations, open ports, security headers, exposed files, known CVEs, and many more common OWASP ans MITRE vulnerabilities.
How long does a scan take?
A full scan can take between 5 and 60 minutes, depending on the perimeter and performance of the target. Rapid scans are completed in less than 5 minutes.
Can I upgrade my plan?
Yes! You can upgrade at any time. Unused credits from credit packs are carried over to your new plan.
Do you support enterprise plans?
Yes! Contact us for custom enterprise pricing with dedicated support, SLAs, and deployment options.
Ready to Secure Your Digital Assets?
Start with a free scan or choose a plan that fits your needs.